In its 2021 Threat Report, Blackberry Cylance released a list of the most dangerous malware plaguing the internet world. The list entailed a certain theme according to which cybercriminals have developed novel ways of exploiting individuals, businesses, and state actors alike by delivering threats through emails and messages.
The Rising Tide of IoT and Threats Associated with It
The increased popularity of the Internet of Things (IoT) devices is worsening the security situation. Most IoT devices flooding the market do not allow their users to change the default username and password, which is a great source of vulnerability, along with no built-in firewall. These chinks in the armor of IoT have led to a whopping 217.5% increase in IoT devices attacks since 2017. Thanks to IoT, your entire household devices have access to your Wi-Fi code, which makes you easy prey for cyber actors on the mission to exploit.
To avert this security disaster, IoT device experts need to work on the concept of a separate core networks and IoT networks and an interface that makes it easier for the user to access multiple networking options in one go.
The Usual Threats
Threats over the web, such as phishing attacks, scams, extortion, identity theft, compromised business-email, harassment, financial, and investment fraud, have remained pretty much the same apart from their level of sophistication, which keeps leveling up. To wrestle with these threats, you must utilize an effective cybersecurity suite, which can be purchased from either a cybersecurity company or your Internet Service Provider. Top ISPs offer free and competent security features such as Charter Spectrum™ does in its famed Spectrum bundles, which can prove quite economical.
The Malware Threat
2021 is seeing rampancy in malware threats that everyone needs to remain aware of in order to stay one step ahead of cybercriminals, who buy or rent out malware services to disrupt other entities and breach their data for their own gains. Here’s a list of top Malware that is disrupting networks and systems for individuals, industries, and governments in 2021:
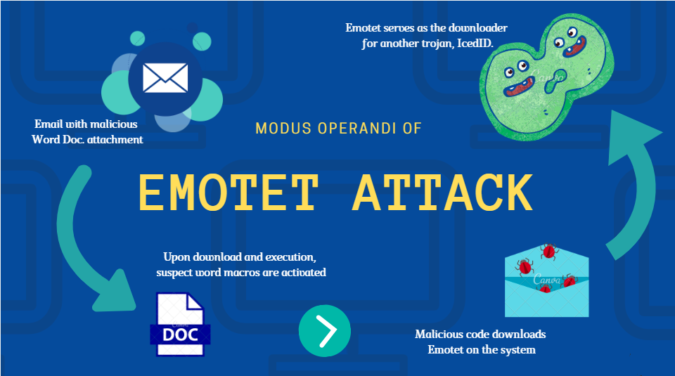
1 Emotet
This malware has been working towards stealing your credentials since 2014, and currently, it works as a delivery mechanism for other malware. It has the characteristics of a virus as once it impacts your system; it keeps spreading with anything that comes into its contact. [Malware for Windows]
2 Kovter
This malware targets your computer’s registry, which makes it harder to detect than others. It initially started as hoax warning ads; now, it has developed into an ad-fraud market, which generates revenue for malware producing businesses. [Malware for Windows]
3 Qakbot
Deadlier than it was a decade ago, it locks user and administrator accounts, which makes it harder to get rid of. [Malware for Windows]
4 Sakurel
The malware can remotely access a machine via malicious URLs. When the target prey access the site, it immediately infects it. The Trojan works as a spy, monitoring the user’s behavior. Once it has completely breached a system, it can be utilized for deadlier attacks. [Malware for Windows]
5 Vercuse
It can infect the machine through random online download and removable storage drives. What makes it pernicious is its ability to avoid detection via several sly methods; one of them is eliminating anti-malware processes upon tool detection. [Malware for Windows]
6 XcodeGhost
The malware is notorious for being the first-ever full-fledged attack on Apple’s App Store, which should caution users to avoid downloading apps from unknown sources. The malware extracts strategic data from an infected device, turning out to be an effective spy. [Malware for Mac and iOS]
7 LaoShu
Remotely accesses machines via infected PDF files. The malware then compresses specific types of files in order to extract them from the machine. [Malware for Mac]
8 NetWiredRC
NetWiredRC is an example of how the lines are blurring between state actors and cybercriminals. The malware is an Iranian state-sponsored remote access Trojan that commits to access sensitive information and credentials from the infected device. [Malware for Mac]
Key Takeaway
The list by Cylance is quite thorough. However, we have extracted the top malware for your perusal. The purpose of the comprehensive list is not only to make you aware but also to spur you into taking precautions to avoid being the target of any malicious attack. To protect yourself, try to use valid VPNs, steer clear of public Wi-Fi, and watch out for unusual registry mods and system boot up.