Are you thinking of expanding your workspace? You’re not alone. Since Jon Peddie Research shed light on how multi-monitors elevate productivity by almost 50%, we’ve been hooked to the Mobile Pixels Trio triple monitor for…
Technology
Technology plays an important role in our life; it is founded in almost everything that surrounds us. Technology participates in every part in our life; and we use all the time and everywhere too (at work, computers, mobile phones, printers and other devices). When you enter your home, directly you will find the technology while watching your television or using your tablet. This Pouted Technology Trends is divided into many sections including the latest and new in robotics, web hosting and software.
As technology continues to advance, the retail industry is witnessing a transformation like never before thanks to the implementation of artificial intelligence (AI). AI, which encompasses technologies like machine learning and data analytics, is revolutionizing…
Voice-activated home features have revolutionized the way we interact with our living spaces. With the rise of smart home automation, voice control devices have become an integral part of modern homes. From voice assistants like…
Welcome to a world where clothing goes beyond mere fabric and becomes a conduit for innovation and connectivity. Smart clothing with built-in technology is revolutionizing the fashion industry, introducing a new era of style, functionality,…
Elon Musk, the renowned tech entrepreneur, has set the tech world abuzz with his latest venture, Project Omega. While many details about this enigmatic project remain undisclosed, the anticipation and speculation surrounding it are palpable.…
In the ever-evolving landscape of digital creativity, image manipulation has undergone a remarkable transformation, thanks to the advent of AI-powered editing tools. These advanced solutions have ushered in a new era of seamless and precise…
Laptops, smartphones, and other types of technology have become a regular part of today’s university life. You use your laptop or smartphone to take notes in class. You also don’t need to visit a physical…
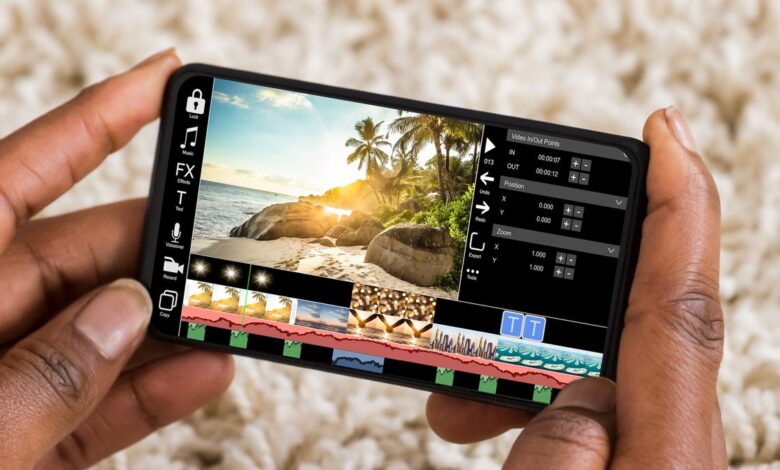
The creation of mobile applications has become an essential tool for organizations looking to increase their reach and engage with their target audience in the ever-changing world of technology. However, one burning question persists –…
Our houses are more than just places to live; they are havens where we seek solace, convenience, and relaxation. The appropriate appliance selection is the key to improving the quality of our home lives. Essential…
So you’ve finally set up your Instagram account and started posting photos, but your likes and followers are still stuck in the single digits. Don’t worry – you’re not alone. Building an engaged following on…